1. Introduction
With insider threats posing a significant challenge in the Health industry, it is imperative to establish rigorous user screening processes that align with Australian Standard 4811-2022 and Protective Security Policy Framework (PSPF) 12, ensuring the security and integrity of commonwealth systems – such as the My Health Record system. This article highlights the importance of adopting such methodologies, taking cues from the effective strategies already employed by other sectors, including the Defence Industry and Critical Infrastructure Sectors.
“No doubt an improved framework would assist in strengthening the protection of Personal Health Information, which is in my view, the most precious piece of information an individual can ever hold, nothing is more personal than what blood type you are, your diagnosis, pathology history and your DNA.” – J.S. Chief Digital Health Officer, IVF Company
2. Insider Threats: A Perturbing Reality
- Resume Inaccuracies: 20% fraudulent, 50% erroneous.
- Malicious Data Breaches: 25% attributed to malicious insiders.
- Organisational Theft: 5% of annual revenue lost to occupational fraud.
- Concealed Criminal Records: 60% not disclosed in interviews, even when asked.
- Illicit Drug Use: 1 in 50 employees use ICE, and 1 in 38 use marijuana illegally.
3. The Economic Impact of Malicious Insider Breaches
In the last 2.5 years, 78% of healthcare providers have experienced at least one data breach. Data breaches orchestrated by malicious trusted insiders, distinct from accidental breaches, present a profoundly damaging scenario. This represents 1 in 4 of all breaches and is proven to be the most expensive type of data breach. These deliberate actions not only tarnish organisational reputation but also come with a hefty price tag. The average annual cost of an incident by malicious insiders was $4.8 million, up from $4.1 million in 2022. Malicious insider incidents are notably expensive: costing on average $701,500 per incident, which is a substantial financial burden that underscores the necessity of preventive measures. Only 8.2 percent of IT security budgets are allocated specifically to insider risk programs and policies. The remaining 91.8 percent of the budget are spent on external threats. Can you see that funding is being inadvertently misdirected due in part to a widespread misunderstanding of insider risks and how they manifest based on early warning behaviours.
“You would never have a business without having a risk assessment. The same thing is critical for the human. A human risk assessment: Where can we be vulnerable?”

Robin Lennon Bylenga, information security specialist, Human Factor Security.
4. Compliance with AS 4811-2022 Workforce Screening
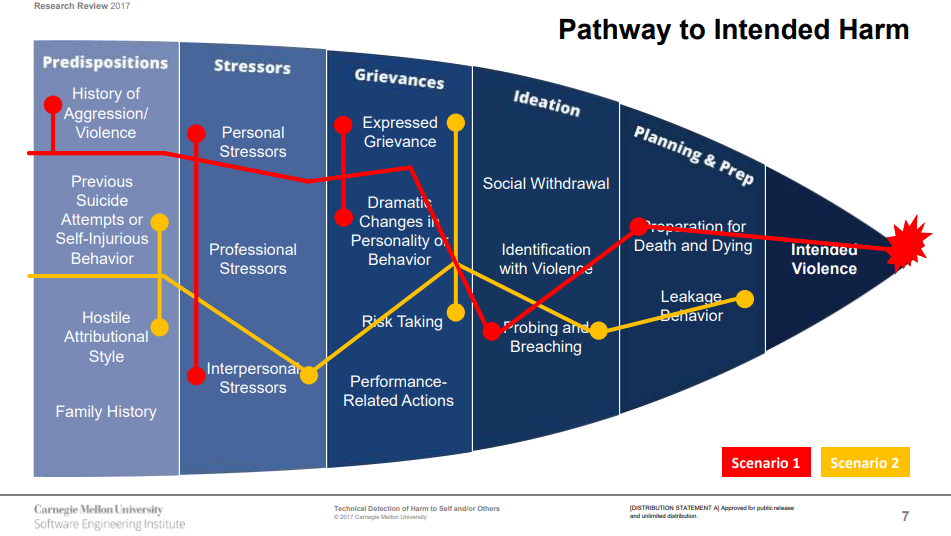
Adhering to AS 4811-2022, which mandates 1:1 interviews and risk assessments by qualified assessors, echoing PSPF12, provides a structured framework for effectively vetting candidates’ predispositions, stressors and behaviours, thereby mitigating risks and safeguarding systems against potential threats.
5. Ensuring Adherence to PSPF 12
The former privacy commissioner Malcolm Crompton said of digital health records that they “will not be secure unless a widespread audit of every GP clinic in Australia is conducted. It may well be military-grade [security] on the central servers of the My Health Record system [but] it’s demonstrably not military grade for all of those 900,000 practitioners.” The Digital Health Record is a Commonwealth system. The PSPF states that anyone who accesses a commonwealth system needs to have their background screened and found ‘suitable‘ before getting access. Further more, every medical practice has more than just this one system that they need to access to do their jobs – those systems will have PII. “Suitable” is a technical term found and defined in the PSPF. Implementing PSPF 12 compliant screening, through tailored Health-centrered, PSPF Compliant Civilian Suitability Clearance, ensures thorough non-discriminatory vetting and adherence to national standards, fortifying security from the inside. A police check alone is not enough. A WWCC is not enough. A Referee Report is not enough. It does not require a new vetting unit (Aged Care Workers Card, NDIS Worker Screening). A Civilian Suitability Clearance can remain at the employer level so they can manage their own risks.
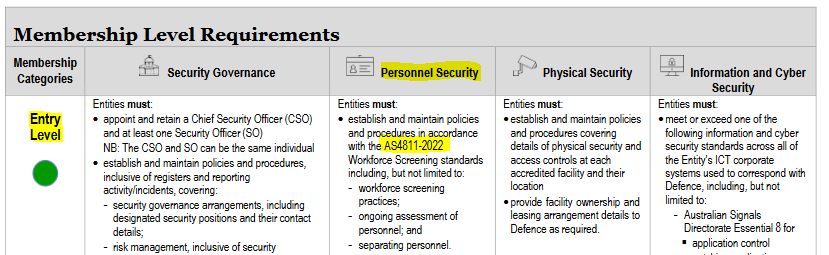
6. Defence Industry: A Pragmatic Exemplar
The Defence Industry’s strategy of mandating AS 4811 for all security cleared and non-security-cleared staff demonstrates a proactive and effective approach to mitigating insider threats and provides a pragmatic employer model for enhancing user screening within commonwealth systems.
7. Recommendations
- Implement AS 4811-2022 and PSPF 12 Compliant Screening: Adopt screening processes in compliance with AS 4811-2022 and PSPF 12.
- Rigorous Background Screening: Employ screening mechanisms that probe, scrutinise historical breaches, drug use and financial stability and more.
- Continuous User Management: Implement ongoing user management strategies, including continuous monitoring and periodic reassessment.
- Enhance Pre-incident Focus: Allocate a larger budget portion towards pre-incident activities and preventative measures.
8. Conclusion
Implementing rigorous user screening processes, compliant with AS 4811-2022 and PSPF 12, is crucial to mitigating insider threats within Commonwealth IT systems that non-Government employees will be accessing. The Hon George Brandis QC says it is fundamental to good business. Considering the substantial financial implications of malicious insider breaches and drawing inspiration from the Defence Industry’s strategies, Critical Infrastructure Personnel Hazards legislation and our solutions: the Defence Suitability Screening, Critical Infrastructure Clearance and Mining Sector Clearance, a Health Sector Clearance provides all the necessary ingredients: standardisation, consistency, compliance, effective and proactive risk mitigation, and sustained operational security within commonwealth systems in the Health sector.
Through the integration of regulatory compliance, statistical insights, and practical recommendations, we present a comprehensive strategy to safeguard commonwealth systems against insider threats. By employing detailed pre-employment screening, continuous user management, and a proactive risk mitigation approach, commonwealth systems can effectively safeguard their operations, ensuring compliance, security, and sustained integrity.